Introduction: The Essential Role of IT Support in Modern Business
In an era where digital technology underpins nearly every facet of organizational operations, IT Support has become far more than a reactive service for troubleshooting computer issues. Businesses today rely on sophisticated IT infrastructures for managing communications, financial transactions, customer relationships, cloud storage, and data analytics. In this context, IT Support plays a critical role in ensuring safety, building trust, and mitigating risks that can threaten the stability of operations. A lapse in IT Support can result in severe consequences, including data breaches, prolonged system downtime, regulatory fines, and loss of customer confidence. Conversely, effective IT support not only resolves technical issues but also strengthens the organization’s resilience, supports strategic goals, and fosters confidence among employees, customers, and stakeholders. As technology continues to evolve, understanding the multifaceted role of IT support is essential for organizations that aim to remain competitive, secure, and reliable in a rapidly changing digital landscape.
IT Support Beyond the Helpdesk
Historically, IT Support was often equated with helpdesk services focused on solving minor technical problems, such as password resets, software installation, and printer configuration. While these tasks remain part of the IT support function, the role has expanded to encompass a wide range of responsibilities critical to organizational success. Modern IT support teams manage enterprise-wide infrastructure, oversee cybersecurity defenses, enforce compliance standards, coordinate disaster recovery strategies, and optimize cloud and network performance. This evolution has transformed IT support into a strategic function that ensures operational continuity while mitigating risks associated with technology use.
Organizations often implement multi-tiered IT support structures to address varying levels of complexity. Level 1 technicians handle common user issues, Level 2 engineers focus on network and server management, and Level 3 specialists or architects design secure infrastructures and manage high-level risk mitigation strategies. Many companies align their IT support practices with internationally recognized frameworks, such as those recommended by the National Institute of Standards and Technology, ensuring consistency, accountability, and resilience across all technology systems. By adopting a structured and proactive approach, IT support transitions from a reactive function into a strategic pillar of organizational risk management.
Cybersecurity: The Core Function of IT Support
Cybersecurity is arguably the most critical component of IT support. In today’s threat landscape, organizations face numerous risks, including ransomware, phishing attacks, insider threats, and advanced persistent attacks. IT support teams serve as the first line of defense, deploying layered security measures to prevent breaches and minimize exposure to malicious activity.
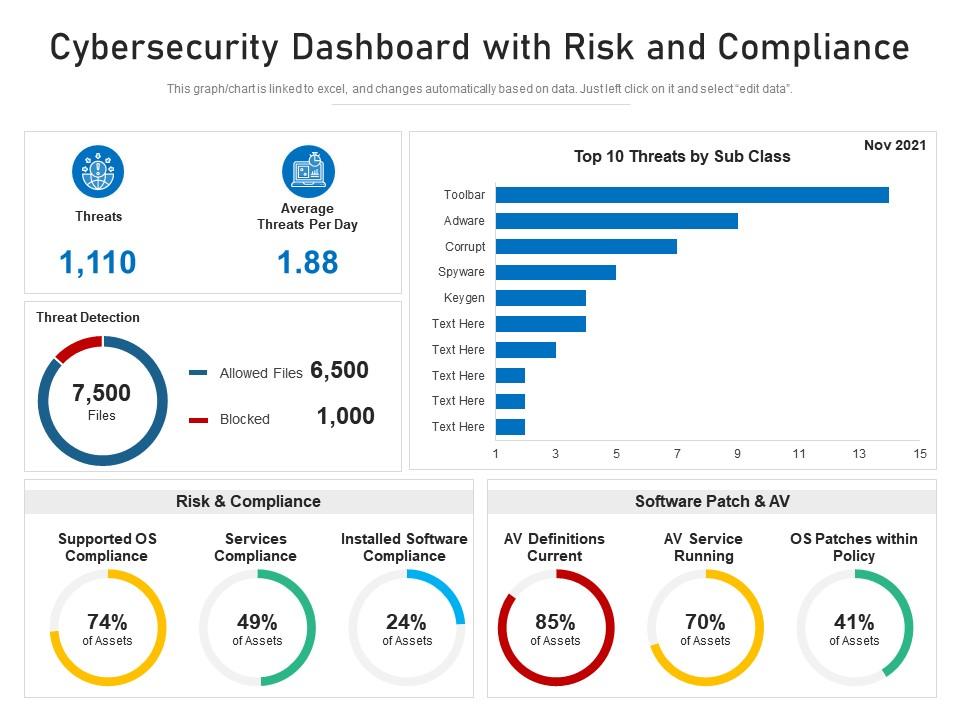

Key cybersecurity strategies include the deployment of firewalls to filter network traffic, intrusion detection and prevention systems to monitor and respond to threats, and endpoint protection software to secure devices connected to corporate networks. Multi-factor authentication strengthens identity verification, reducing the risk of unauthorized access. Encryption of sensitive data ensures confidentiality both in storage and during transmission.
Continuous monitoring through Security Operations Centers (SOCs) allows IT support teams to detect anomalies in real time, enabling immediate response to potential security breaches. Routine vulnerability assessments, penetration testing, and timely patch management further strengthen defenses. By adopting these proactive measures, IT support reduces the likelihood of incidents, ensuring business operations remain secure and uninterrupted.
Infrastructure Reliability and Building Trust
Trust in modern business operations is built on system reliability and consistent service delivery. Customers and partners expect uninterrupted access to applications and secure management of their data, while employees rely on stable IT systems to perform their duties efficiently. IT support ensures the reliability of infrastructure by maintaining servers, optimizing network performance, and managing redundancy systems designed to prevent downtime.
Cloud platforms such as Amazon Web Services and Microsoft Azure provide scalable, secure environments for business operations. However, achieving high availability requires proper configuration, continuous monitoring, and proactive maintenance. IT support teams oversee backup scheduling, load balancing, and failover mechanisms to prevent disruptions and maintain system performance.
Reliable infrastructure is essential not only for operational continuity but also for establishing digital trust. Consistent uptime, quick issue resolution, and secure handling of data demonstrate competence and professionalism, enhancing organizational reputation and fostering confidence among stakeholders.
Risk Management and Disaster Recovery Planning
IT support also plays a pivotal role in risk management and disaster recovery planning. Beyond cybersecurity, organizations face operational risks from hardware failures, natural disasters, human errors, and power outages. Identifying vulnerabilities and implementing mitigation strategies are essential for reducing the impact of such events on business continuity.
Disaster recovery involves defining Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs), which establish acceptable downtime and data loss thresholds. IT support teams manage offsite backups, cloud replication, and redundant network systems to facilitate rapid recovery. Regular testing of recovery plans ensures preparedness for unexpected incidents.
Business continuity planning complements disaster recovery by ensuring critical functions continue during a disruption. This includes communication protocols, workflow alternatives, and contingency plans to maintain service delivery. Organizations that integrate robust IT support into risk management strategies can withstand disruptions while minimizing financial and reputational damage.
Securing Remote and Hybrid Work Environments
The rise of remote and hybrid work models has increased the complexity of IT support responsibilities. Employees now access corporate systems from multiple locations and devices, creating additional vulnerabilities that require careful management. IT support teams implement security protocols to protect distributed networks and ensure that remote operations are safe and compliant.

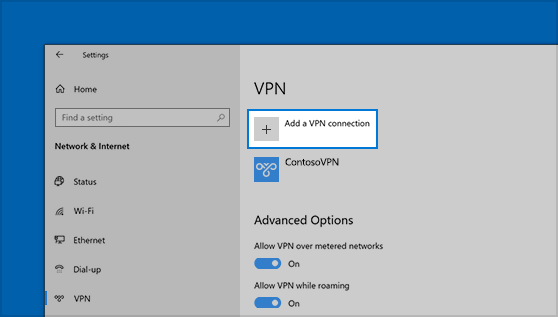
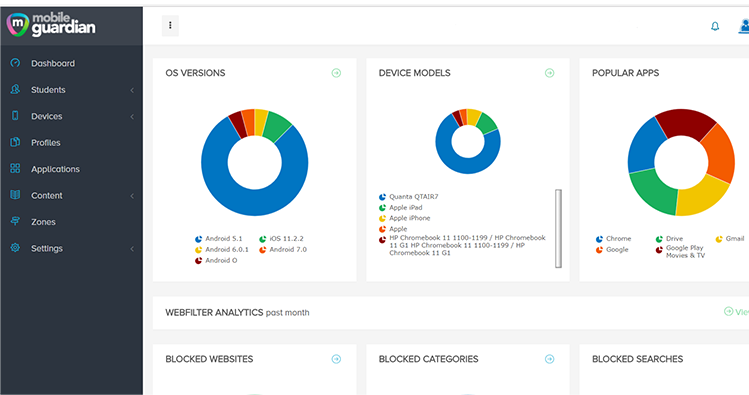
Virtual Private Networks (VPNs) encrypt data transmission over public networks, while mobile device management (MDM) systems enforce security policies on laptops, tablets, and smartphones. Multi-factor authentication protects against unauthorized access, and remote wipe capabilities safeguard sensitive information if devices are lost or stolen.
By implementing standardized protocols for both in-office and remote workers, IT support ensures flexibility without compromising security. This balance is essential for maintaining productivity while minimizing risk in modern work environments.
Compliance, Governance, and Ethical Responsibility
Compliance with data protection regulations has become increasingly important in a global business environment. Organizations must adhere to local and international standards to avoid fines and protect their reputation. IT support ensures compliance by monitoring access to sensitive data, implementing proper storage practices, and maintaining detailed documentation of security measures.
Beyond legal obligations, ethical responsibility is central to building trust. Customers and partners expect organizations to handle their data responsibly. IT support contributes to ethical governance by enforcing policies, auditing systems, and providing transparency in operations, which reinforces credibility and long-term trust.
Human Factors and Security Awareness
Even with advanced technology, human error remains a leading cause of security incidents. IT support teams address this challenge by educating employees on cybersecurity best practices. Training programs cover phishing prevention, password management, safe handling of sensitive data, and proper use of IT systems.
Encouraging employees to report suspicious activities and follow security protocols creates a culture of awareness and accountability. When staff actively participate in maintaining digital security, IT support becomes a collaborative process that strengthens overall organizational resilience.
Future Trends in IT Support
The future of IT support is closely linked to technological innovation. Artificial intelligence and machine learning are increasingly being used to monitor systems, detect anomalies, and automate routine tasks. Predictive analytics allow IT teams to anticipate and prevent issues before they escalate, while zero-trust architectures enforce continuous verification of devices and users, enhancing security in distributed environments.
Automation reduces the burden of repetitive tasks, freeing IT professionals to focus on strategic initiatives, cybersecurity improvements, and infrastructure optimization. Continuous adaptation ensures that IT support remains effective in the face of evolving threats and technological changes.
Conclusion: IT Support as a Pillar of Safety, Trust, and Risk Protection
IT Support is no longer a supplementary function; it is a strategic necessity for modern organizations. By combining cybersecurity defenses, infrastructure reliability, disaster recovery planning, compliance management, and human awareness programs, IT support ensures organizational resilience, operational continuity, and stakeholder trust. Companies that invest in robust IT support frameworks not only protect their assets but also gain a competitive advantage through increased reliability and customer confidence. In an increasingly interconnected and risk-prone world, IT support serves as the essential foundation for safety, trust, and sustainable business growth.
 Roberta Heathc
Roberta Heathc